Introduction
- The connection from a Controller to an Agent can be secured by HTTPS.
- This article describes the steps required to set up secure HTTPS communication from a Controller to an Agent. This includes to use a standalone Controller or a Controller cluster with a primary and standby instance.
- Consider the JS7 - System Architecture for an overview of components and connections.
- Consider to set up JS7 - JOC Cockpit HTTPS Connections for secure connections from clients (user browser / REST API client) to JOC Cockpit.
- Consider JS7 - Controller HTTPS Connections for securing the connections between JOC Cockpit and Controller instances.
Prerequisites
- Certificate stores can be managed from the command line and by use of tools that provide a GUI for this purpose:
- the Java Keytool is available from the Java JRE or JDK,
- the Keystore Explorer is an open source utility to graphically manage certificate stores.
Certificate Management
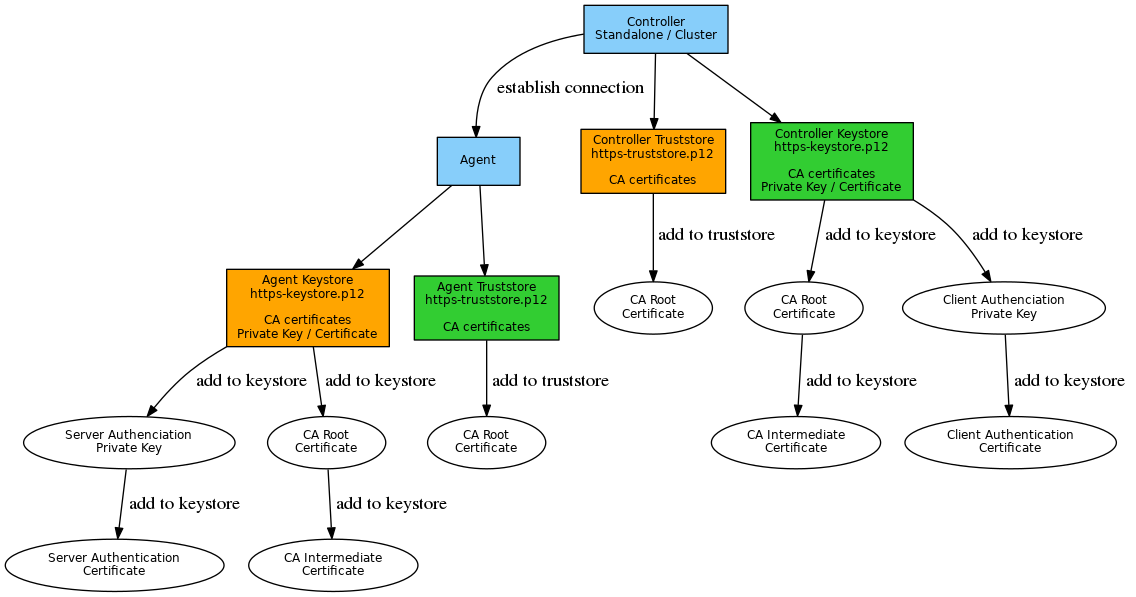
Private keys and public certificates should be distributed as follows:
Explanation:
- Keystore and truststore in orange color are required for any connections of a Controller to an Agent.
- The Agent's private key and certificate for Server Authentication are added to the Agent's keystore. In case of a self-signed certificate the certificate is added to the Controller truststore too.
- This step can be skipped if a CA-signed certificate is used as the Root Certificate in the Controller truststore is sufficient to verify Agent certificates.
- Keystore and truststore in green color are required if mutual authentication is in place for certificate based client authentication (default).
Secure Connection Setup
In the following the placeholder JS7_CONTROLLER_CONFIG_DIR specifies the configuration directory of the Controller. The placeholders JS7_AGENT_HOME, JS7_AGENT_CONFIG_DIR specify the directories where the Agent is installed and configured.
- JS7_CONTROLLER_CONFIG_DIR is the Controller's configuration directory that is specified during Controller installation:
/var/sos-berlin.com/js7/controller/config(default on Linux)C:\ProgramData\sos-berlin.com\js7\controller\config(default on Windows)
JS7_AGENT_HOMEis the installation path that is specified during the JobScheduler Agent installation:/opt/sos-berlin.com/js7/agent(default on Linux)C:\Program Files\sos-berlin.com\js7\agent(default on Windows)
JS7_AGENT_CONFIG_DIRis the Agent's configuration directory that is specified during Agent installation:/var/sos-berlin.com/js7/agent/config(default on Linux)C:\ProgramData\sos-berlin.com\js7\agent\config(default on Windows)
Set up a Secure Connection to the Agent
Step 1: Create the Agent Keystore
- On the Agent server create the keystore using the
keytoolfrom your Java JRE or JKD. Alternatively import a certificate that you received from your certificate authority:- Generate the keystore with the private key and public certificate for the Agent and export the certificate to a second keystore that is later on used by the Master or use the attached script keygen.sh to perform this task. The below examples suggest one possible approach for certificate management, however, there may be other ways how to achieve similar results.
Example for use of CA-signed certificate:
Example for use of CA signed certificate: export Agent private key and Agent public certificate# should your Agent private key and certificate by provided with a .jks keystore (keypair.jks) then temporarily convert the keystore to pkcs12 (keystore.p12) # for later use with openssl, assuming the alias name of the Agent private key is "agent-https" # keytool -importkeystore -srckeystore keypair.jks -destkeystore keystore.p12 -deststoretype PKCS12 -srcalias agent-https # assuming your Agent private key from a pkcs12 keystore (keystore.p12), store the Agent private key to a .key file in PEM format (agent-https.key) openssl pkcs12 -in keystore.p12 -nocerts -out agent-https.key # concatenate CA root certificate and CA intermediate certificate to a single CA Bundle certificate file (ca-bundle.crt) cat RootCACertificate.crt > ca-bundle.crt cat CACertificate.crt >> ca-bundle.crt # Export Agent private key (agent-https.key), Agent certificate (agent-https.crt) and CA Bundle in PEM format (ca-bundle.crt) to a new keystore (https-keystore.p12) # assume the fully qualified hostname (FQDN) of the Agent server to be agent.example.com openssl pkcs12 -export -in agent-https.crt -inkey agent-https.key -chain -CAfile ca-bundle.crt -name agent.example.com -out JS7_AGENT_CONFIG_DIR/private/https-keystore.p12 # should you require use of a .jks keystore type then convert the pkcs12 keystore assuming the alias name of the Agent private key to be "agent-https" # keytool -importkeystore -srckeystore agent-https.p12 -srcstoretype PKCS12 -destkeystore JS7_AGENT_CONFIG_DIR/private/https-keystore.jks -deststoretype JKS -srcalias agent-https
Example for use of self-signed certificate:
Example for use of self-signed certificate: generate Agent private key and export Agent public certificate# generate the Agent's private key with alias name "agent-https" in a keystore (https-keystore.p12) # use the fully qualified hostname (FQDN) and name of your organization for the distinguished name keytool -genkey -alias "agent-https" -dname "CN=hostname,O=organization" -validity 1461 -keyalg RSA -keysize 2048 -keypass jobscheduler -keystore "JS7_AGENT_CONFIG_DIR/private/https-keystore.p12" -storepass jobscheduler -storetype PKCS12 # export the Agent's certificate to a file in PEM format (agent-https.crt) keytool -exportcert -rfc -noprompt -file "agent-https.crt" -alias "agent-https" -keystore "JS7_AGENT_CONFIG_DIR/private/https-keystore.p12" -storepass jobscheduler -storetype PKCS12
- if you choose an individual password for the Agent Keystore then adjust the following properties in the
<agent_data>/config/private/private.confconfiguration file:- Explanations
jobscheduler.agent.webserver.https.keystore.fileis used for the path to the Keystorejobscheduler.agent.webserver.https.keystore.passwordis used for the Keystore passwordjobscheduler.agent.webserver.https.keystore.key-passwordis used for the password of your private HTTPS certificate
Example
Example for private.conf file with keystore specificationjobscheduler.agent.webserver.https.keystore { file = "C:/ProgramData/sos-berlin.com/jobscheduler/agent110/config/private/private-https.jks" # Backslashes are written twice (as in JSON notation): # file = "\\\\other-computer\\share\\my-keystore.jks" password = "jobscheduler" key-password = "jobscheduler" }
- Explanations
- For the Master the Truststore that contains the Agents' public certificate is expected with the password
jobscheduler.
- Generate the keystore with the private key and public certificate for the Agent and export the certificate to a second keystore that is later on used by the Master or use the attached script keygen.sh to perform this task. The below examples suggest one possible approach for certificate management, however, there may be other ways how to achieve similar results.
- On the JobScheduler Agent server store the Keystore with the private key in the directory
<agent_data>/config/private- Default file name:
private-https.jks
- Default file name:
- On the JobScheduler Master server store the Truststore with the public certificate of the Agent in the directory
<master_data>/config- Default file name:
agent-https.jks FEATURE AVAILABILITY STARTING FROM RELEASE 1.13.3The location, type and password of the Master Truststore can be specified:
Example for specification of Master Truststore with Agent public certificatesjobscheduler.master.agents.https.keystore { file = "/var/sos-berlin.com/jobscheduler/apmaccs_4444/config/agent-https.p12" # Backslashes are written twice (as in JSON notation): # file = "\\\\other-computer\\share\\my-keystore.jks" password = "jobscheduler" key-password = "jobscheduler" }Example for import of an Agent public certificate to a Master Truststore in pkcs12 format:
Example for import of Agent public certificate to a pkcs12 Master Truststore# import Agent public certificate to a truststore (agent-https.p12) by specifying the Agent public certificate file (agent-https.crt) and alias name (agent-https) keytool -importcert -noprompt -file "agent-https.crt" -alias "agent-https" -keystore "SCHEDULER_DATA/config/agent-https.p12" -storepass jobscheduler -storetype PKCS12 -trustcacerts
Example for import of an Agent public certificate to a Master Truststore in jks format (specifying the default values for location, type and password):
Example for import of Agent public certificate to a jks Master Truststore# import Agent public certificate to a truststore (agent-https.p12) by specifying the Agent public certificate file (agent-https.crt) and alias name (agent-https) keytool -importcert -noprompt -file "agent-https.crt" -alias "agent-https" -keystore "SCHEDULER_DATA/config/agent-https.jks" -storepass jobscheduler -trustcacerts
- Default file name:
Step 2: Set up authentication between Master and Agent
- On the JobScheduler Master server configure the Master password in a file on the Master in the
<master_data>/config/privatedirectory:- File name:
private.conf The file should contain the following entry that specifies a plain text password
myjobscheduler4444that is used by the Master to authenticate against Agents:Example for Master private.conf file with Master password specificationjobscheduler.master.credentials.password = "myjobscheduler4444"
- File name:
- On the JobScheduler Agent server specify the same Master password in a file in the directory
<agent_data>/config/private- File name:
private.conf Specify the Master that will authenticate with the Agent by its JobScheduler ID and password. For example, for two Masters with JobScheduler ID
scheduler_4444andscheduler_5555this file would look like this assuming that the Master password ismyjobscheduler4444:Example for Agent private.conf file with specification of Master Scheduler ID and passwordjobscheduler.agent.auth.users { scheduler_4444 = "plain:myjobscheduler4444" scheduler_5555 = "sha512:9184ddcaa87eb2f95c32f12741035c1e55cef93f7834905f926c4bc419fbc5613e2e141d39fb05d0ec7c66c9bd9e4c8b95b74598e0107f863b7f2bd942a9aea0" }- For each entry the JobScheduler ID is used as key, the value (in double quotes) includes the hash algorithm followed by a colon and the hashed password.
- Using
plainfor the hash algorithm requires a plain text password to be specified. Use of plain text passwords is not recommended as they could be visible to jobs running on that Agent. - Using
sha512for the hash algorithm requires a password that is hashed with the respective algorithm. A number of command line utilities to create an sha512 hash from a plain text password can easily be found.
- Using
- File name:
Step 3: Start the Agent for HTTPS
- On the JobScheduler Agent server start the Agent with the corresponding parameters:
- Example (using port 44445 for HTTPS):
<agent_data>/bin/jobscheduler_agent -https-port=44445 - The HTTP port will always be used, even if the Agent is started for communicating over HTTPS. If no HTTP port is indicated when starting the Agent, then the default port (4445) will be used. The reason for this behavior is the requirement that the Agent can be locally controlled by its start script without further need for authentication.
- HTTPS has to be indicated when starting an Agent by use of the parameter
-https-port. - The Agent requires a data directory for configuration files and temporary files The data directory has to be indicated when starting the Agent by using the parameter
-data-directory. - The above mentioned parameters can be specified as environment variables with the Agent instance script, see Installation & Operation.
- Example (using port 44445 for HTTPS):
Notes
- A restart of the respective component is required to apply modifications to .the
JS7_AGENT_CONFIG_DIR/private/private.conffile of the Agent andJS7_CONTROLLER_CONFIG_DIR/private/private.conffile of the Controller respectively.