Introduction
- Connections from user browsers to JOC Cockpit can be secured by HTTPS and TLS/SSL certificates.
- Connections from clients using the JS7 - REST Web Service API (that ships with JOC Cockpit) can be secured by HTTPS TLS/SSL certificates.
- This article describes the steps required to set up secure HTTPS communication with JOC Cockpit. This includes to set up a standalone JOC Cockpit instance or a JOC Cockpit cluster with a number of instances.
- Consider the JS7 - System Architecture for an overview of components and connections.
- Consider JS7 - Controller HTTPS Connections for securing the connections between JOC Cockpit and Controllers.
- Consider JS7 - Agent HTTPS Connections for securing the connections between Controller instances and Agents.
Prerequisites
- Certificate stores can be managed from the command line and by use of tools that provide a GUI for this purpose:
- the Java Keytool is available from the Java JRE or JDK,
- the Keystore Explorer is an open source utility to graphically manage certificate stores.
Certificate Management
To secure access to JOC Cockpit by clients (user browsers or REST API clients) the following keys and certificates should be in place:
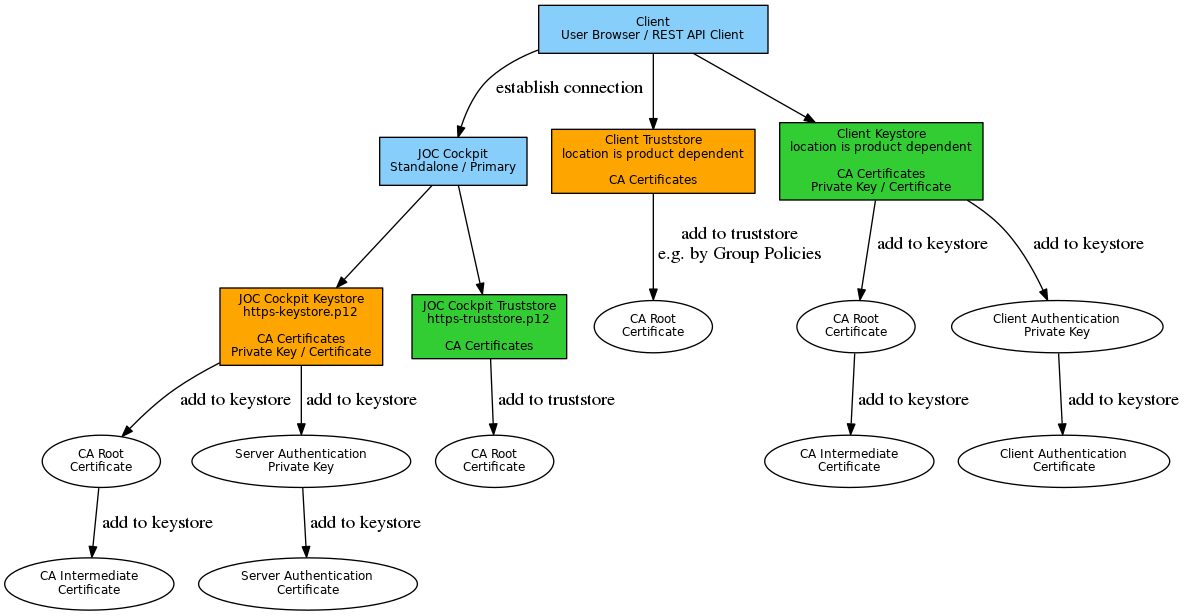
Explanation:
- Keystore and truststore in orange color are required for any connections of clients to JOC Cockpit.
- Keystore and truststore in green color are required if mutual authentication is in place, e.g. to allow certificate based authentication.
- A JOC Cockpit truststore in green color is required should secure connections be used to access a Controller or an LDAP server for authentication/authorization. It is therefore recommended to set up the JOC Cockpit truststore.
- Consider that similar distribution of private keys and certificates applies if a JOC Cockpit cluster with a number of instances is used.
Secure Connection Setup
In the following the placeholders JOC_HOME, JETTY_HOME and JETTY_BASE are used which locate three directories. If you install Jetty with the JOC Cockpit installer then
JOC_HOMEis the installation path that is specified during JOC Cockpit installation:/opt/sos-berlin.com/js7/joc(default on Linux)C:\Program Files\sos-berlin.com\js7\joc(default on Windows)
JETTY_HOME=JOC_HOME/jettyJETTY_BASEis Jetty's base directory that is specified during JOC Cockpit installation:/home/<setup-user>/sos-berlin.com/js7/joc(default on Linux)C:\ProgramData\sos-berlin.com\js7\joc(default on Windows)
Secure Connections for Clients to JOC Cockpit
This configuration is applied in order to enable clients (user browser, REST API client) to access the JOC Cockpit by use of HTTPS.
Step 1: Add the HTTPS module to Jetty
On the JOC Cockpit server run the following command and replace the
JETTY_HOMEandJETTY_BASEplaceholders as specified above:Add HTTPS module to Jettyjava -jar "JETTY_HOME/start.jar" -Djetty.home="JETTY_HOME" -Djetty.base="JETTY_BASE" --add-to-start=https
- Having executed the above command you should find a new folder
JETTY_BASE/etcJetty expects a Keystore in this folder with the name "keystore" by default.
Jetty doesn't start if it doesn't find a keystore corresponding its settings.
- In addition a number of entries in the
JETTY_BASE/start.iniconfiguration file for TLS/SSL settings such as the HTTPS port are added.
Step 2: Create the Keystore for Jetty
- On the JOC Cockpit server create the keystore using the
keytoolfrom your Java JRE or JDK or some third party utility.- For use with a third party utility create a keystore, e.g.
https-keystore.p12,in PKCS12 format and import:- JOC Cockpit private key and certificate for Server Authentication
- Root CA certificate
- Intermediate CA certificates
- For use with
keytoolgenerate the keystore in JKS or PKCS12 format with the private key and certificate for JOC Cockpit Server Authentication. The below examples suggest one possible approach for certificate management, however, there may be other ways how to achieve similar results.Example for import of CA signed certificate to a PKCS12 keystore:
Example how to add a CA signed certificate to a PKCS12 Keystore# should the JOC Cockpit's private key and certificate be provided with a .jks keystore (keypair.jks) then temporarily convert the keystore to pkcs12 (keystore.p12) # for later use with openssl, assuming the alias name of the JOC Cockpit private key being "joc-https" # keytool -importkeystore -srckeystore keypair.jks -destkeystore keystore.p12 -deststoretype PKCS12 -srcalias joc-https # assuming your JOC Cockpit private key from a pkcs12 keystore (keystore.p12), store the JOC Cockpit private key to a .key file in PEM format (joc-https.key) openssl pkcs12 -in keystore.p12 -nocerts -out joc-https.key # concatenate CA Root certificate and CA Intermediate certificates to a single CA Bundle certificate file (ca-bundle.crt) cat RootCACertificate.crt > ca-bundle.crt cat CACertificate.crt >> ca-bundle.crt # Export JOC Cockpit private key (joc-https.key), JOC Cockpit certificate (joc-https.crt) and CA Bundle (ca-bundle.crt) in PEM format to a new keystore (https-keystore.p12) # assume the fully qualified hostname (FQDN) of the JOC Cockpit server being "joc.example.com" openssl pkcs12 -export -in joc-https.crt -inkey joc-https.key -chain -CAfile ca-bundle.crt -name joc.example.com -out "JETTY_BASE/resources/joc/https-keystore.p12" # should you require use of a .jks keystore type then convert the pkcs12 keystore assuming the alias name of the JOC Cockpit private key being "joc-https" # keytool -importkeystore -srckeystore https-keystore.p12 -srcstoretype PKCS12 -destkeystore https-keystore.jks -deststoretype JKS -srcalias joc-https
Example for use of self-signed certificate with a PKCS12 keystore
Example how to generate a self-signed certificate for import into a PKCS12 Keystore# generate JOC Cockpit private key with alias name "joc-https" in a keystore (https-keystore.p12) # use the fully qualified hostname (FQDN) and name of your organization for the distinguished name # consider that PKCS12 keystores require to use the same key password and store password keytool -genkey -alias "joc-https" -dname "CN=hostname,O=organization" -validity 1461 -keyalg RSA -keysize 2048 -keypass jobscheduler -keystore "JETTY_BASE/resources/joc/https-keystore.p12" -storepass jobscheduler -storetype PKCS12
Example for use of self-signed certificate with a JKS keystore
Example how to generate a self-signed certificate for import into a JKS Keystore# generate JOC Cockpit private key with alias name "joc-https" in a keystore (https-keystore.jks) # use the fully qualified hostname (FQDN) and name of your organization for the distinguished name keytool -genkey -alias "joc-https" -dname "CN=hostname,O=organization" -validity 1461 -keyalg RSA -keysize 2048 -keypass jobscheduler -keystore "JETTY_BASE/resources/joc/https-keystore.jks" -storepass jobscheduler -storetype JKS
Explanation:
- Replace the
JETTY_BASEplaceholder as specified above. - The
-dnameoption specifies the certificate issuer, therefore use your own set of CN, OU, DC that specify the issuer's distinguished name. The O setting is required for the issuer. - The
-keypassoption accepts the password that you will need later on to manage your private key. - The
-keystoreoption specifies the location of your Keystore file. - The
-storepassoption specifies the password for access to your Keystore file. - The
-storepassoption is used for the PKCS12 keystore format, this option is not required for the JKS keystore format.
- Replace the
- For use with a third party utility create a keystore, e.g.
- Alternatively apply a private key and certificate that are issued by your certificate authority or a trusted authority.
Step 3: Configure Jetty
See below chapter Step 2: Configure Jetty for configuration of the truststore with JETTY_BASE/start.ini.
Edit the following entries in the
JETTY_BASE/start.iniconfiguration file use of the keystore:## Keystore file path (relative to $jetty.base) jetty.sslContext.keyStorePath=resources/joc/https.keystore.p12 ## Keystore password jetty.sslContext.keyStorePassword=jobscheduler ## KeyManager password (same as keystore password for pkcs12 keystore type) jetty.sslContext.keyManagerPassword=jobscheduler
Explanation:- Specify the location of the keystore with the
keyStorePathsetting. A location relative to theJETTY_BASEdirectory can be specified. - Specify the password for your keystore with the
keyStorePasswordsetting. - The password specified with the
keyManagerPasswordsetting is used for access to your private key. The same password as for thekeyStorePasswordsetting has to be used for a PKCS12 keystore type.
- Specify the location of the keystore with the
Specify the HTTPS port with the following entry of the
JETTY_BASE/start.iniconfiguration file (default HTTPS port is 48446):## Connector port to listen on jetty.ssl.port=48446
Step 4: Deactivate HTTP Access
To deactivate HTTP access add a comment to the following module directive in your JETTY_BASE/start.ini configuration file like this:
# Module: http # --module=http
Mutual Authentication for Clients to JOC Cockpit
This configuration is applied in order to enable mutual authentication:
- the client verifies the JOC Cockpit certificate for Server Authentication
- JOC Cockpit verifies the client certificate for Client Authentication
Step 1: Add the Truststore to Jetty
- On the JOC Cockpit server create the truststore using the
keytoolfrom your Java JRE or JDK or some third party utility.- For use with a third party utility create a truststore, e.g.
https-truststore.p12,in PKCS12 format and import:- Root CA certificate
- For use with
keytoolcreate the truststore in JKS or PKCS12 format with the Root CA certificate. The below examples suggest one possible approach for certificate management, however, there may be other ways how to achieve similar results.Example for import of a Root CA certificate to a PKCS12 truststore
Example how to import a CA signed certificate into a PKCS12 Truststore# import Root CA certificate in PEM format to a PKCS12 truststore (https-truststore.p12) keytool -import -alias "root-ca" -file "RootCACertificate.crt" -keystore "JETTY_BASE/resources/joc/https-truststore.p12"
- For use with a third party utility create a truststore, e.g.
Step 2: Configure Jetty
See above chapter Step 3: Configure Jetty for configuration of the keystore with JETTY_BASE/start.ini.
Edit the following entries in the
JETTY_BASE/start.iniconfiguration file use of the keystore:## Truststore file path (relative to $jetty.base) jetty.sslContext.trustStorePath=resources/joc/https-truststore.p12 ## Truststore password jetty.sslContext.trustStorePassword=jobscheduler
Explanation:- Specify the location of the truststore with the
trustStorePathsetting. A location relative to theJETTY_BASEdirectory can be specified. - Specify the password for access to the truststore with the
trustStorePasswordsetting.
- Specify the location of the truststore with the
Specify the settings to enforce client authentication with the following entries in the
JETTY_BASE/start.iniconfiguration file:## force use of client authentication certificates jetty.sslContext.needClientAuth=false jetty.sslContext.wantClientAuth=true jetty.sslContext.endpointIdentificationAlgorithm=
Explanation:
- Find explanations from the JS7 - Authentication article.
Notes
- A restart of JOC Cockpit is required to apply modifications to the JOC Cockpit
JETTY_BASE/start.iniandJETTY_BASE/resources/joc/joc.propertiesconfiguration files .